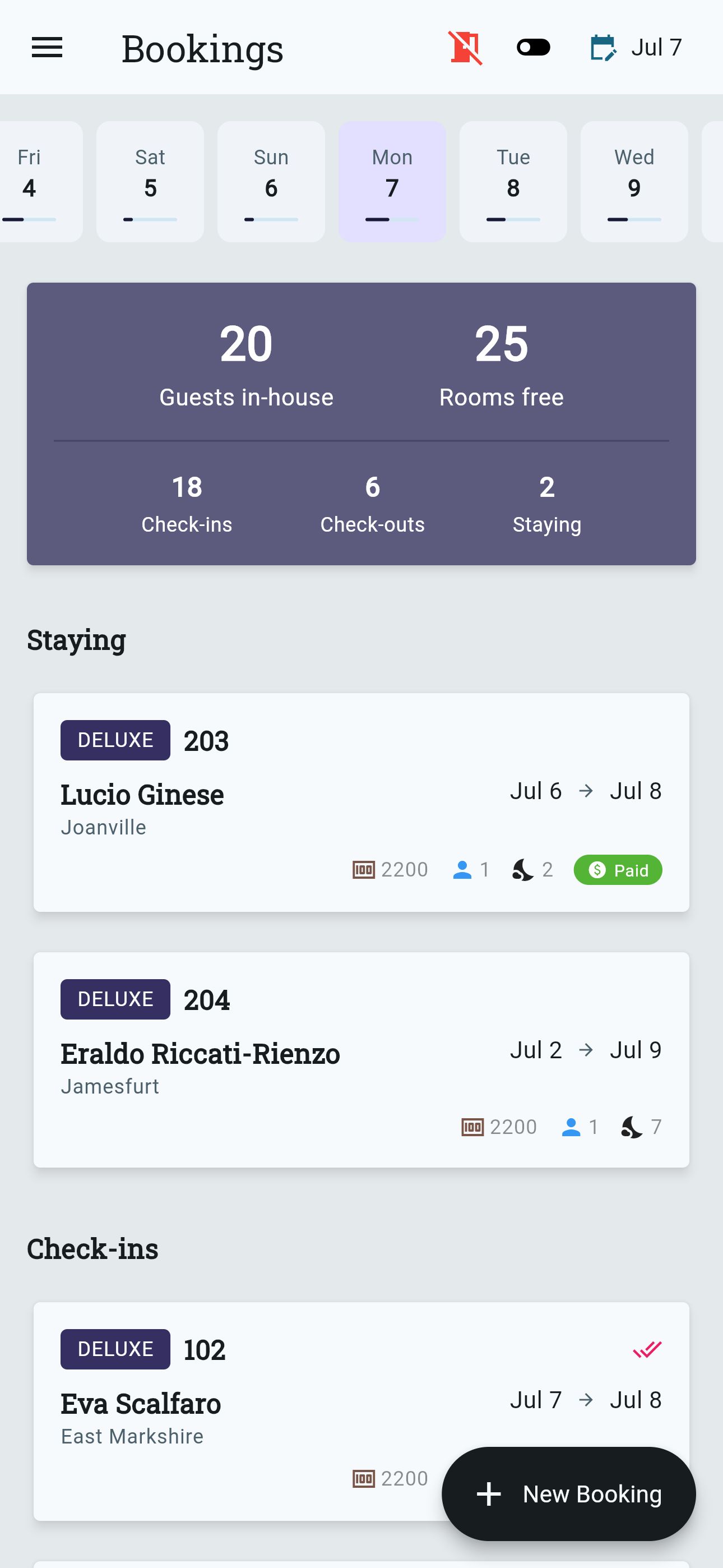
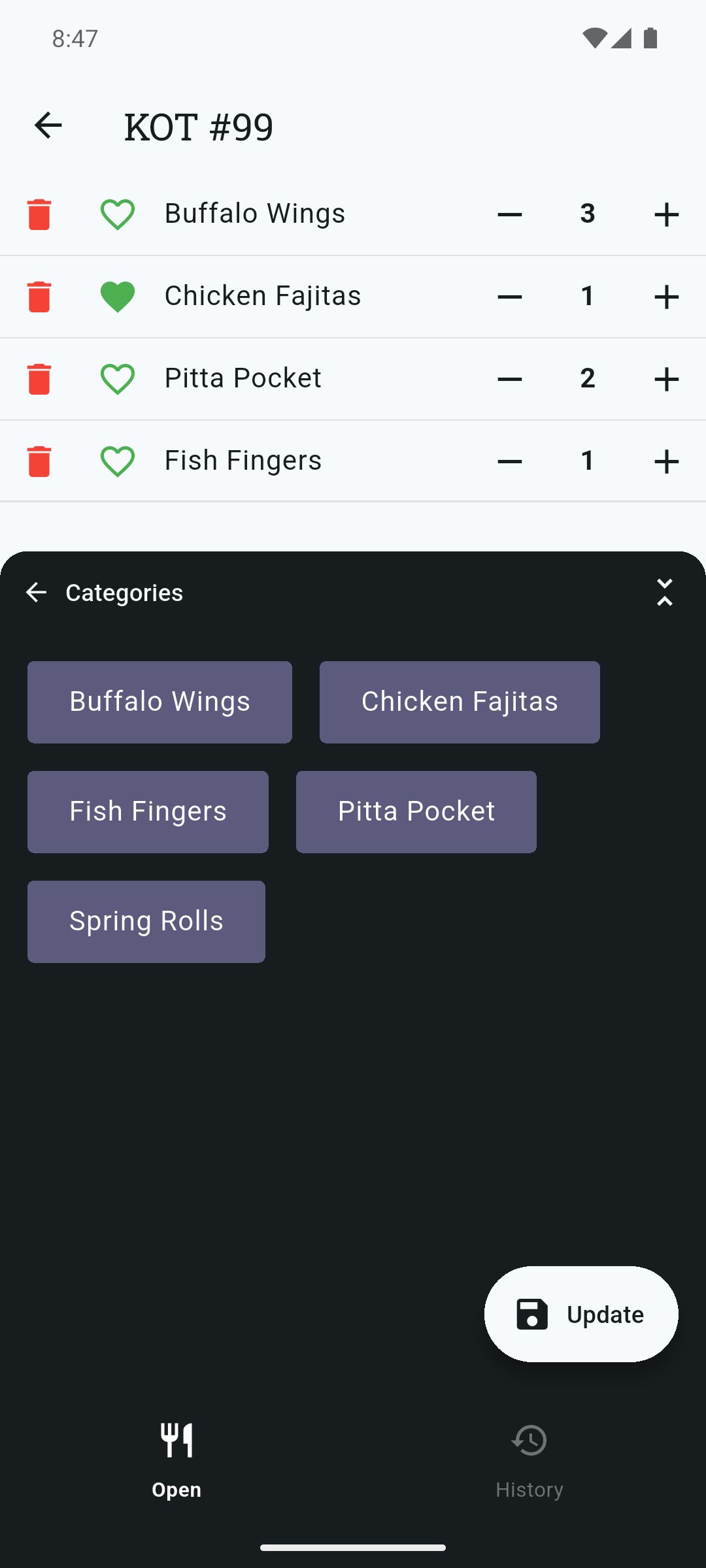
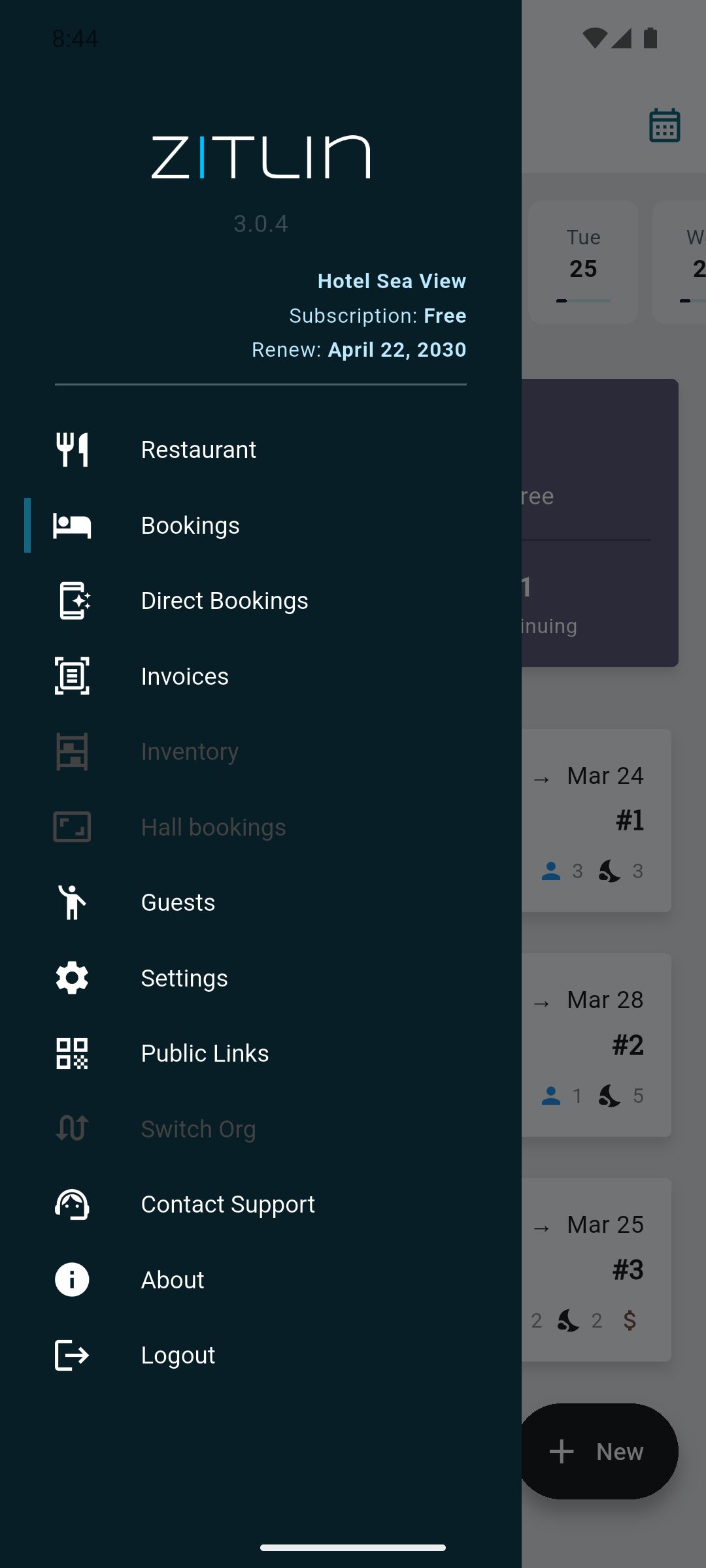
Effortlessly Manage Your Hotel & Restaurant Business
Say goodbye to lengthy onboarding processes. With Zitlin, you can self-onboard and complete your first check-in in just 10 minutes!
Say goodbye to lengthy onboarding processes. With Zitlin, you can self-onboard and complete your first check-in in just 10 minutes!
 |
 |
 |
 |
 |
 |
 |
 |
: This is a social engineering attack where hackers use fake QR codes to steal active Telegram sessions. Attackers generate a "login" QR code from the official Telegram Web interface and trick users into scanning it with their mobile app. Once scanned, the attacker gains full access to the user's Telegram account—including any surveillance feeds or bots.
: Keep your IP cameras on a separate Wi-Fi network from your main devices. If a camera is compromised via a QR exploit, the attacker’s access to your personal data will be restricted. Talos Vulnerability Report ip camera qr telegram patched
: Some IP cameras use QR codes for initial setup or network provisioning. Researchers have discovered vulnerabilities (such as those in certain Yi Home Camera models ) where a specially crafted QR code can cause a buffer overflow . If an attacker shows a malicious QR code to your camera, they could potentially execute code remotely and take over the device. : This is a social engineering attack where
The keyword "" refers to a specific intersection of smart home surveillance and cybersecurity vulnerabilities. While often used as a search term for users seeking to fix security flaws in their Internet Protocol (IP) cameras or Telegram-based monitoring bots, it highlights several critical security risks—and the essential patches required to secure them. Understanding the Vulnerabilities : Keep your IP cameras on a separate
: Manufacturers release firmware updates to patch hardware-level vulnerabilities like QR buffer overflows. Visit the support page for your specific brand (e.g., Yi Technology or TP-Link ) to download and install the latest security updates.
: Never scan a QR code sent by an unknown bot or displayed on an untrusted website to "verify" your identity.
: If you use a DIY bot (like those for Raspberry Pi or ESP32-CAM ), ensure your code uses updated libraries. Developers frequently push security fixes to GitHub repositories to address API-related flaws. Best Practices for Secure Monitoring